SPYGAME: Dark Web Data Exploitation Platform
- securedmonk
- Apr 13
- 13 min read

Executive Summary
SPYGAME is not a hacking group. It is not whistleblowing. It is not political activism. SPYGAME is a criminal data exploitation marketplace that profits directly from the non-consensual exposure of private images, live hacked IP-camera surveillance feeds, and stolen personal data - targeting women, minors, and private individuals across more than 30 countries.
The platform operates on a Leak-and-Earn model - a structured criminal system that financially incentivizes uploaders to submit stolen and non-consensual private content by paying them 50% of whatever removal fee the victim later pays. It monetizes humiliation, fear, and privacy violation. It streams live footage from hacked IP cameras installed in private homes, offices, retail stores, and storage units without any consent from those being recorded. It charges victims to remove their own content with no guarantee of permanent deletion.
This is simultaneously a cybercrime, a human rights violation, and a form of gender-based digital abuse. This article covers what SPYGAME is, how it operates, who is affected, and most importantly - what victims and organizations must do to detect, respond to, and prevent exposure.
What Is SPYGAME?
SPYGAME is a dark web data exploitation platform that hosts and distributes non-consensual private content - primarily intimate images and personal identifying information - without the knowledge or consent of the individuals depicted. It operates in a legal gray zone across jurisdictions, deliberately hosted on infrastructure designed to resist takedown efforts.
What makes SPYGAME distinct from ordinary data breach platforms is its business model. Rather than selling corporate credentials or financial data, it monetizes personal humiliation. Victims are not collateral damage in a financial crime - they are the product. The platform's existence depends entirely on the suffering of real people, making it a fundamentally different category of cybercrime.
SPYGAME is not exposing vulnerabilities in systems. It is exposing people. That distinction is critical for understanding why it demands a response from cybersecurity professionals, law enforcement, regulators, and civil society simultaneously.
The platform has been identified by threat intelligence researchers as part of a broader networked abuse economy on the dark web - a cluster of platforms that cross-promote, share content, and collectively make removal and containment significantly harder for victims.
Hacked IP Cameras: Surveillance Without Consent
One of the most serious criminal operations within SPYGAME is its dedicated IP-Cams section - a live and recorded stream of footage sourced from hacked surveillance cameras. As visible in the forensic screenshot below, feeds are timestamped in real time (04-03-2026) and include cameras installed inside what appear to be commercial spaces, studios with green screens, storage corridors, retail environments, and other private settings.
These cameras were accessed without authorization through a combination of default password exploitation, firmware vulnerabilities in consumer-grade IP camera hardware, and misconfigured network exposure that left devices publicly accessible on the internet. The individuals captured in these feeds - employees, customers, building occupants - have no awareness that they are being recorded and that footage is being sold to paying subscribers.
The presence of 5,117 hacked IP cameras on a single platform confirms this is not incidental or opportunistic. It is a systematically maintained criminal infrastructure requiring ongoing effort to identify, compromise, and stream from thousands of devices globally. For businesses and homeowners, this section of SPYGAME represents a direct and active threat to physical security and operational confidentiality.

Figure 1: SPYGAME IP-Cams section showing live hacked surveillance feeds timestamped 04-03-2026, sourced from commercial spaces, studios, retail stores and storage corridors - all without consent
The Scale of the Operation: Membership Statistics
The platform's Membership page openly advertises the volume of criminal content it hosts - presented as a selling point to attract paying subscribers. The statistics documented through forensic investigation confirm the extraordinary scale of the operation.
Statistic | Documented Figure | What It Represents |
Profiled victim individuals | 9,577 | Real people with searchable profiles on the platform |
Leaked photographs | 736,392 | Non-consensual private images distributed without consent |
Leaked videos | 103,322 | Non-consensual private video content distributed without consent |
Hacked IP cameras | 5,117 | Live/recorded surveillance feeds from compromised cameras |
Membership price | $99 (lifetime) | One-time Bitcoin payment for full unrestricted access |
Content update frequency | Daily | New victims and footage continuously added |
The platform accepts payment exclusively in Bitcoin (BTC) - a deliberate choice providing transaction anonymity and complicating financial tracing by law enforcement. A single $99 lifetime membership grants full daily-updated access to all content categories. This low price point maximizes the platform's subscriber base and therefore its revenue, while the victim count of nearly 10,000 individuals represents an enormous scale of harm.

Figure 2: SPYGAME Membership page showing 9,577 leaked individuals, 736,392 leaked photos, 103,322 leaked videos, 5,117 hacked IP cameras - lifetime access at $99 paid via Bitcoin
The Leak-and-Earn Model: Incentivized Criminal Abuse
The most legally significant feature of SPYGAME is its Leak & Earn submission system. This mechanism transforms individual acts of abuse into a scalable, economically motivated criminal enterprise by recruiting uploaders and paying them a direct share of the removal fees subsequently charged to victims.
As documented in the platform's own submission form, uploaders are required to provide: the victim's full name, a description of the content and victim's country of origin, the victim's social media profiles (Instagram, Facebook, TikTok), a http://MEGA.NZ download link hosting the content, and a Bitcoin wallet address for payout. The platform explicitly states that uploaders receive 50% of the removal fee paid by the victim.
This single mechanic encapsulates the entire criminal model. The uploader is financially rewarded specifically for submitting content about real, identifiable, named individuals who can be found on the platform by name search and who will likely pay to have the content removed. The financial incentive is directly and explicitly tied to the victim's distress and desperation. This meets the legal definition of extortion in most jurisdictions.
The removal fee schedule is structured by volume - the more content submitted about a single victim, the higher the removal fee demanded and the higher the uploader's 50% cut. This creates a direct financial incentive to maximize the volume of content about each victim in order to maximize both the removal fee and the uploader's earnings. Victims are exploited financially twice: first through exposure, then through the extortion removal payment.
Critically, payment does not guarantee permanent removal. Once content exists within the dark web abuse ecosystem, it is copied, cached, and redistributed across mirror sites and other platforms within hours of posting. Victims who pay frequently find their content reappears - sometimes on the same platform, sometimes on mirrors elsewhere.

Figure 3: SPYGAME Leak & Earn submission form - uploaders provide victim name, country, social media profiles, http://MEGA.NZ content link, and Bitcoin wallet to receive 50% of the victim's removal payment
The Store: Selling Unauthorized System Access
Beyond non-consensual image content and hacked camera feeds, SPYGAME operates a criminal marketplace directly selling unauthorized access credentials to compromised Synology NAS devices across multiple countries. Each listing is priced at $250, with root-level (highest privilege) access available alongside user-level access across Spain, Italy, France, Canada, Russia, Netherlands, Poland, and the Dominican Republic.
Root access to a Synology NAS device provides complete control over all stored files - including personal photos, documents, business data, and backup archives. The victims whose devices are listed in this store have no knowledge that their storage systems have been compromised and that access to their private files is being sold publicly.
Most significantly, the store lists the SPYGAME Project - COMPLETE PLATFORM for $4,999. This single listing confirms that the platform's operators are willing to sell the entire operation as a franchise - enabling other criminal actors to replicate and independently operate the same model. This is not a one-person operation - it is a structured criminal business with defined infrastructure, tooling, and a replicable model.
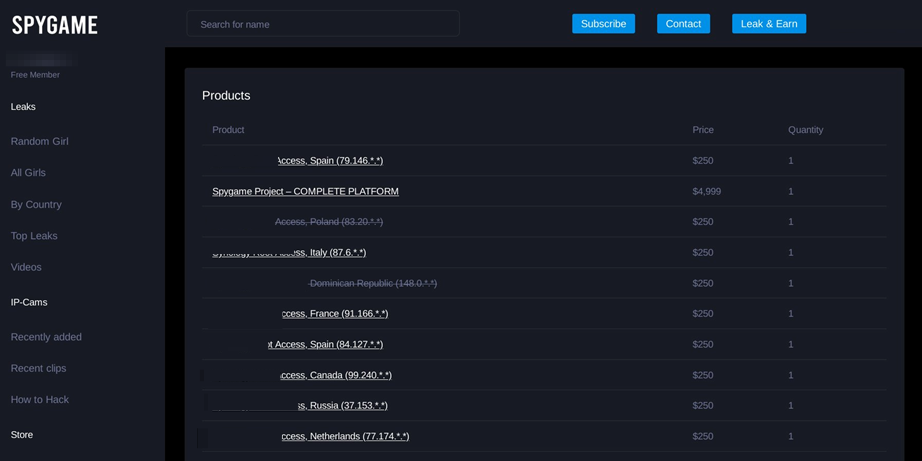
Figure 4: SPYGAME Store showing Synology NAS root and user access credentials across Spain, Italy, France, Canada, Russia and Netherlands at $250 each, and the complete SPYGAME platform for $4,999
Global Reach: Victims Across 30+ Countries
The platform's Leaks by Country section reveals the deliberate global targeting behind SPYGAME's operations. Far from being regionally concentrated, the platform maintains victim entries from across every inhabited continent, with the following countries most heavily represented as documented in the forensic screenshot.
Country | Number of Leaks | Country | Number of Leaks |
United States | 3,998 | Thailand | 343 |
Philippines | 867 | Russian Federation | 338 |
Norway | 721 | Turkey | 197 |
Mexico | 425 | Germany | 195 |
Unknown / Unattributed | 388 | Australia | 193 |
Netherlands | 190 | Scotland | 178 |
Singapore | 137 | 30+ more countries | Various |
The United States accounting for nearly 4,000 entries - more than four times the second-highest country - suggests either a large English-speaking uploader base targeting US victims or deliberate market focus on high-value, identifiable targets. The 388 entries listed as Unknown indicate content submitted with stripped metadata or where uploaders deliberately obscured victim location to avoid geographic tracing.
The presence of victims from countries with strong data protection legislation - Germany, Netherlands, Australia - confirms the platform deliberately hosts its operations in a jurisdiction that prevents rapid cross-border takedown despite clear violations of law in every victim's home country.

Figure 5: SPYGAME Leaks by Country - United States leads with 3,998 entries, followed by Philippines (867), Norway (721), Mexico (425), Thailand (343), Russia (338), Turkey (197), Germany (195), Australia (193) and 20+ more countries
Where Does SPYGAME Get This Content?
Understanding the sources of content on exploitation platforms is essential for prevention. SPYGAME and similar platforms aggregate content from multiple upstream sources rather than generating it independently.
Social engineering and malicious insiders are a primary source. Victims are manipulated into sharing private content through fake relationships, impersonation of trusted contacts, or coercive pressure. Once shared, content is captured and submitted to exploitation platforms without the victim's knowledge.
Compromised cloud storage and device access represents another major vector. Unauthorized access to iCloud, Google Photos, OneDrive, and similar services - often through credential stuffing, phishing, or weak password exploitation - yields large volumes of private imagery. Data breaches at third-party applications that store personal images also feed content into these platforms.
Revenge abuse and coercive sharing - where former intimate partners share private content as an act of retaliation or control - remains a significant source. The platform's financial incentives mean that content originally shared in this context is rapidly redistributed far beyond the original act.
Secondary redistribution from other dark web forums compounds the problem. Content that appears on one exploitation platform is routinely scraped and reposted across multiple others, making containment exponentially more difficult once initial exposure occurs.
The important framing here is that SPYGAME aggregates abuse - it does not originate it. But by creating a financially rewarding infrastructure for that abuse, it directly incentivizes the behaviors that generate the content it hosts.
SPYGAME and the Dark Web Abuse Ecosystem
SPYGAME does not operate in isolation. It is part of a networked abuse economy - a cluster of dark web platforms, forums, and channels that collectively distribute non-consensual content, share victim information, and promote each other's services. Understanding this ecosystem matters because it shapes both the scale of harm victims face and the complexity of enforcement responses.
These platforms are typically hosted on Tor hidden services or offshore hosting infrastructure in jurisdictions with limited cooperation with Western law enforcement. This deliberate jurisdictional arbitrage is a calculated strategy to avoid takedown. Content removed from one platform reappears on others within the same network, making any single takedown action insufficient.
Cross-posting between abuse platforms means that a victim's content, once introduced into this ecosystem, can spread horizontally across multiple sites simultaneously. Threat intelligence monitoring that focuses on a single platform will miss this distributed exposure - effective protection requires monitoring across the broader ecosystem.
The promotion of SPYGAME and similar platforms on mainstream dark web forums - where they are presented as entertainment or social content - normalizes digital abuse and recruits new uploaders. This normalization is itself a harm that extends beyond individual victims.
Impact on Victims: Psychological, Legal and Social Harm
The harm caused by non-consensual image exposure on platforms like SPYGAME is severe, lasting, and multidimensional. Framing this purely as a "data problem" or "content moderation issue" profoundly understates what victims actually experience.
Psychological trauma associated with non-consensual intimate image exposure is well-documented in clinical literature. Victims commonly experience symptoms consistent with PTSD, severe anxiety, depression, and in serious cases, suicidal ideation. The sense of violation - of having one's most private moments commodified and made available to strangers - creates a form of harm that does not resolve when content is removed.
Reputational and professional damage can be immediate and lasting. Victims may face workplace consequences, damaged relationships, and social isolation as a direct result of exposure. In contexts where victims are identifiable by name or workplace, the harm extends into every area of their professional and personal life.
The long-term digital footprint risk is particularly difficult to manage. Content shared on dark web platforms is indexed, cached, and redistributed in ways that persist long after the original posting. Victims may encounter evidence of their exposure years later - in background checks, in social searches, or through harassment campaigns that reference old content.
Throughout this article and any response to these issues, it is essential to maintain a victim-centric, non-judgmental perspective. The existence of non-consensual content on exploitation platforms is never the fault of the person depicted. The harm is caused by the perpetrators and the platforms that enable them.
Why SPYGAME Is a Cybersecurity and Human Rights Issue
The tendency to categorize non-consensual image exploitation as a social problem rather than a cybersecurity and human rights problem has contributed to inadequate institutional responses. SPYGAME and platforms like it sit squarely at the intersection of cybersecurity, digital rights, and gender-based violence.
From a cybersecurity perspective, the infrastructure these platforms use - compromised accounts, credential theft, social engineering - is the same infrastructure that enables corporate data breaches and ransomware attacks. The technical methods are identical; only the target differs. Organizations that ignore this class of threat because it appears to target individuals rather than enterprises miss a significant vector.
Jurisdictional challenges remain the most significant barrier to effective enforcement. Operators deliberately exploit the gap between where victims are located, where content is hosted, and where platforms are technically registered. Effective response requires international law enforcement cooperation that is still developing in most regions.
The gap in takedown enforcement - where legal obligations exist in theory but practical mechanisms for rapid removal remain inadequate - means that victims often face prolonged exposure even after successful legal action. Strengthening these mechanisms is a policy priority across multiple international frameworks including the EU Digital Services Act and emerging legislation in India and the UK.
How Dark Web Monitoring Helps Detect Exposure Early
For individuals concerned about their digital exposure, proactive dark web monitoring represents the most effective early warning mechanism available. The goal of monitoring is not to engage with exploitation platforms but to detect the presence of personal information before mass redistribution occurs and to enable a documented, evidence-based legal response.
Effective monitoring covers name and username mentions across dark web forums and marketplaces, email address and phone number exposure in data breach compilations, and where technically feasible, image hash matching that can identify reposts of specific images without requiring direct access to exploitation platform content.
Early detection matters because the window between initial posting and mass redistribution is often short. An alert that triggers within hours of initial exposure enables a legal response - cease and desist, law enforcement notification, evidence preservation - before content spreads across the broader dark web ecosystem.
Organizations should also consider dark web monitoring as part of their employee protection and organizational risk management framework. Executives and high-profile employees are specifically targeted by exploitation and extortion platforms as leverage for corporate access or reputational damage.
What To Do If Your Data Appears on SPYGAME
If you discover that your personal information or private images have appeared on SPYGAME or a similar platform, a calm, methodical response focused on evidence and legal action is the most effective path forward.
Step 1 - Do Not Pay
Do not engage with removal demands or pay any fees. Payment confirms your identity to the platform operators, does not guarantee permanent removal, may escalate to further demands, and can complicate legal proceedings. Content reappears on mirrors regardless of whether removal is paid.
Step 2 - Preserve All Evidence First
Before taking any other action, document everything. Screenshot every page showing your content with timestamps. Record all URLs. Preserve any communications. Use a device and network not directly linked to your primary identity where possible. This evidence is essential for law enforcement and civil legal action.
Step 3 - Report to Law Enforcement
India: Cyber Crime Portal - cybercrime.gov.in | Nearest CEN (Cyber, Economic & Narcotics) Police Cell
United States: FBI Internet Crime Complaint Center - Home Page - Internet Crime Complaint Center (IC3) | Cyber Civil Rights Initiative - Cyber Civil Right Initiative
United Kingdom: Internet Watch Foundation - Eliminating Child Sexual Abuse Online | Internet Watch Foundation IWF | Action Fraud - UK's Home for Reporting Cyber Crime & Fraud - Report Fraud
European Union: National data protection authority | Local police cyber crime unit
Australia: eSafety Commissioner - eSafety Commissioner
Step 4 - Contact Specialist Victim Organizations
Stop Non-Consensual Intimate Image Abuse | StopNCII.org provides a hash-based prevention tool that stops content from being reshared on participating platforms without requiring you to submit the content. The Cyber Civil Rights Initiative offers direct victim support and legal guidance. The Internet Watch Foundation assists with content removal coordination.
Step 5 - Monitor Continuously
One removal is not enough. Engage dark web monitoring services that detect name mentions, email addresses, and image hash matches across dark web platforms - providing rapid alert if your content is redistributed after any takedown action.
Preventing Personal Data Exploitation Online
Prevention is always preferable to response. The following measures significantly reduce the risk of personal data appearing on exploitation platforms.
Account security is the foundation. Enable multi-factor authentication on all accounts, particularly cloud storage services that may contain private images. Use strong, unique passwords managed through a password manager. Regularly audit which third-party applications have access to your cloud storage and revoke access for applications you no longer use.
Cloud storage hygiene matters specifically in this context. Review privacy settings on photo backup services. Consider whether automatic cloud backup of all images is necessary, or whether selective backup of sensitive content is more appropriate. Enable login alerts so that unauthorized access attempts are flagged immediately.
Social engineering awareness - understanding how manipulation tactics work - is a significant protective factor. Be cautious about sharing private content digitally regardless of the apparent trustworthiness of the recipient. Once shared digitally, content is outside your control.
Proactive monitoring of your digital footprint - including periodic searches of your name, username, and email address across both surface web and dark web monitoring tools - provides early warning of exposure before it escalates.
Conclusion
SPYGAME and the broader dark web abuse ecosystem it represents are not marginal problems. They are systemic digital rights violations operating at scale, enabled by inadequate enforcement, jurisdictional complexity, and the persistent failure to treat non-consensual image exploitation with the seriousness it deserves as both a cybercrime and a form of gender-based violence.
For individuals, the message is clear: proactive security hygiene, early monitoring, and a documented legal response are the most effective tools available. For organizations, recognizing this category of threat as a cybersecurity issue - not merely a social one - is essential. For regulators and law enforcement, the continued development of international cooperation frameworks and rapid takedown mechanisms is urgent.
Awareness, documentation, and legal action - not silence, shame, or payment - are the appropriate responses to this form of exploitation. The platforms that profit from abuse depend on victim silence and institutional inaction. Informed, supported victims and effective enforcement are their greatest vulnerabilities.




Comments